Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 92 Posts
- 223 Comments

Otoh, the Washington Post and their “experts” didn’t think any of those civil rights movement direct actions they’re celebrating now were reasonable at the time either 🤡

 2·22 days ago
2·22 days agoIf you’re ready to break free of Android, I would recommend https://postmarketos.org/ though it only works well on a small (but growing!) number of devices.
imho if you want to (or must) run Android and have (or don’t mind getting) a Pixel, Graphene is an OK choice, but CalyxOS is good too and runs on a few more devices.

 31·22 days ago
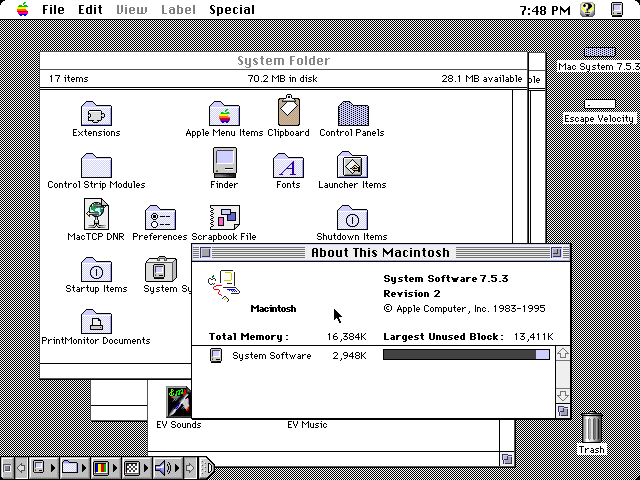
31·22 days agoi guess maybe if you’re using a device with a tiny screen and a lemmy client that doesn’t let you zoom in on images

 3·22 days ago
3·22 days agoIt’s literally a covert project funded by google to both sell pixels and harvest data of “privooocy” minded users. It seems to be working well.
Is it actually funded by Google? Citation needed.
I would assume Graphene users make up a statistically insignificant number of Pixel buyers, and most of the users of it I’ve met opt to use it without any Google services.

 1163·23 days ago
1163·23 days agoshoutout to the person who reported this post with “Reason: Bot meme, you can’t even read it. whoever replies is a bot too” 😂

 16·25 days ago
16·25 days agoYou may not like it, but this is what peak performance looks like.

 25·1 month ago
25·1 month ago/r/shittyaskredditwasn’t supposed to be an instruction manual 🙄

 2·1 month ago
2·1 month agoE: old thinkpad gang input: take the time to reapply thermal grease to the cpu at some point. It makes a huge difference.
What’s a “gang input”?
😂 it’s an input to this discussion from a member of the group of people (“gang”) who have experience with old thinkpads. and yes, if your old thinkpad (or other laptop) is overheating and crashing, reapplying the thermal paste is a good next step after cleaning the fans.

 31·1 month ago
31·1 month ago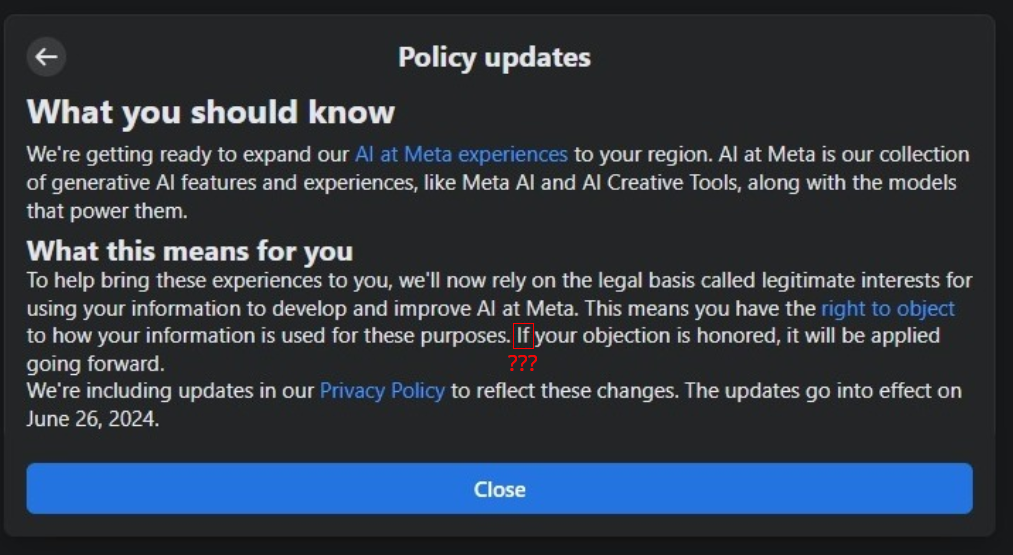
If your objection is honored, it will be applied going forward

 2·1 month ago
2·1 month agoIndeed, the only thing WhatsApp-specific in this story is that WhatsApp engineers are the ones pointing out this attack vector and saying someone should maybe do something about it. A lot of the replies here don’t seem to understand that this vulnerability applies equally to almost all messaging apps - hardly any of them even pad their messages to a fixed size, much less send cover traffic and/or delay messages. 😦

 18·2 months ago
18·2 months agoand later it will turn out that the AI solution was actually two clickworkers in a trenchcoat

 5·2 months ago
5·2 months agoxzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with
systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to rundebootstrap, you just want to specify a snapshot URL likehttps://snapshot.debian.org/archive/debian/20240325T212344Z/in place of the usual Debian repository url (typicallyhttps://deb.debian.org/debian/).

 26·2 months ago
26·2 months agoA daily ISO of Debian
testingor Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.




















lol, i just accepted the title tag from the page which the create post form auto-filled 🤡